Between January 2020 and July 2021, 32 percent of cyberattacks that targeted supply chain businesses resulted in data theft and breaches of internal processes. Supply chain security failures can cost businesses proprietary information, customer trust, and even downtime leading to loss of revenue. To better protect your business, choose supply chain management (SCM) software with robust security features or integrate it with cybersecurity tools. The following list provides options for both.
To find secure supply chain management software that will meet your business needs, use our Product Selection Tool for SCM. After answering some questions about your organization, you’ll get a short, personalized list of software recommendations.
SCM software with strong security
Businesses looking to secure their supply chain should consider SCM software that includes encryption, data isolation, single sign-on (SSO), and similar security measures.
SAP Supply Chain

SAP Supply Chain includes multi-factor authentication (MFA) and SSO, along with role-based access to verify users’ identities and ensure they only have access to what they need. Once a month, SAP also releases patch notes that highlight the latest upgrades to their security features and recommendations for any actions users need to take. Automated auditing and fraud detection tools are also available to improve both security and compliance.
Zoho Inventory
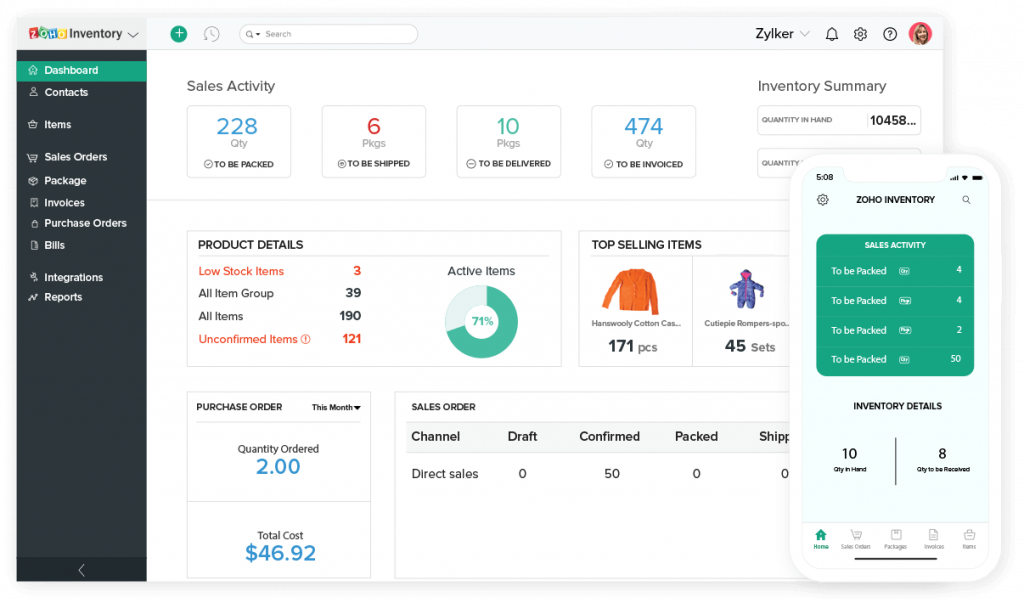
Zoho Inventory uses 256-bit Advanced Encryption Standard (AES) to secure data at rest and during transit, all connections to the Zoho servers require Transport Layer Security (TLS 1.2/1.3) encryption. Additionally, each company’s data is isolated to keep other organizations from accidentally (or purposefully) accessing data that isn’t theirs. In terms of access controls, Zoho Inventory offers single sign-on and MFA to verify a user’s identity before they get access to the system.
Unleashed
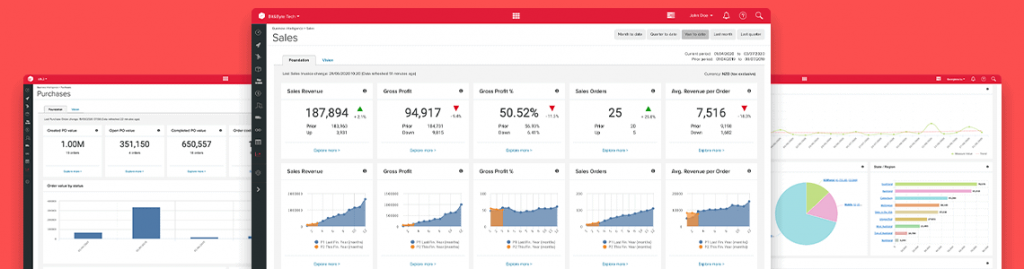
Unleashed employs cloud-based security that replicates customers’ data each day, with backups available in case a server crashes. TLS protocol encrypts traffic during transfer to prevent attackers from intercepting data. Role-based permissions allow users to access only the features they need for their job, while the account lockout feature automatically locks a user’s account after they attempt to log in incorrectly five times. Unleashed also includes two-factor authentication during sign-in.
SAS Supply Chain
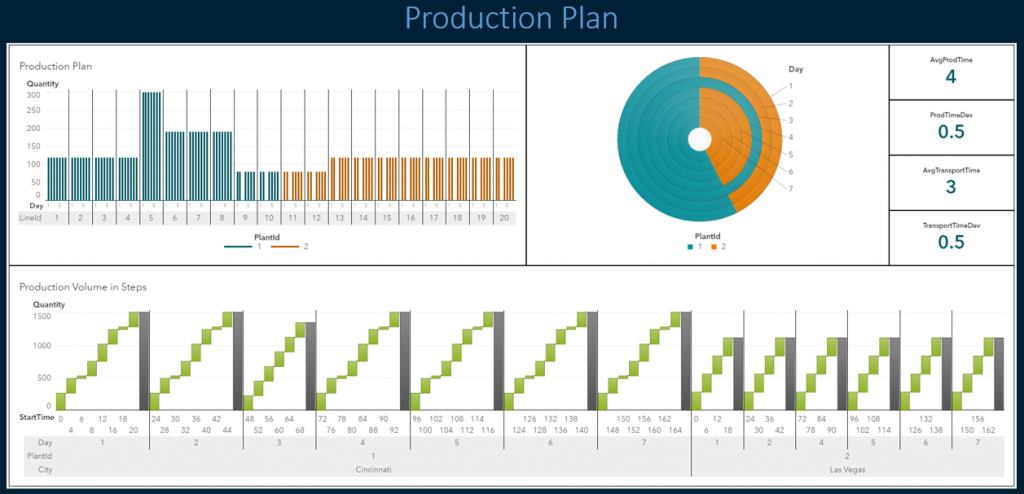
During development, SAS engages both internal and external penetration testers to search for vulnerabilities in its software and then patches them before rolling the product out to the public. Data is encrypted both in transit and at rest, and SSO allows users to easily access the features they need without leaving the system vulnerable. For mobile connections, system administrators will have to whitelist a user’s device, allowing them to safely access the system from their smartphone.
Standalone cybersecurity tools for supply chains
You might already have the perfect supply chain software in place and just need to make sure it’s secure. If that’s the case, consider integrating it with one or more of these cybersecurity tools.
Also Read: Why Free Antivirus Software Won’t Cut it for Your Business
Other methods of securing your supply chain
Software security is important, but human error is one of the main causes of data breaches. Train your employees on the importance of cybersecurity, and help them recognize phishing and smishing attempts, so they can avoid them. You also need to make sure that you’re applying software updates and patches when they roll out. Patches fix new or newly discovered vulnerabilities, meaning you’re putting your company at risk every day you don’t install them.
Our Supply Chain Management Product Selection Tool is free to use, and it takes as little as five minutes. Once you’ve filled out the short survey, you’ll get a customized list of supply chain management software recommendations suited to your business needs.
Read Next: Benefits of Integrating ERP with IoT