What is a web application firewall?
A web application firewall (WAF) is a
security tool that monitors web traffic to protect users from web-based attacks. It acts as an extra layer of protection between the user and the internet, preventing unauthorized data from leaving web applications while blocking malicious traffic from getting in. Businesses can install a WAF directly onto their devices or purchase a subscription to a
firewall-as-a-service (FWaaS). For businesses without many in-house technical resources, FWaaS is probably the better option, since the vendor will handle updates.
Approximately
43 percent of all data breaches originate from web applications, and it’s unlikely that attackers will look for other vectors since this number has doubled since 2019. To protect users as they engage with web applications, businesses need a web application firewall (WAF). A WAF monitors traffic on the web and protects against common attacks, like cross-site scripting and SQL injection.
Find your new web application firewall software
Compare the best web app firewalls of 2022
Each of the tools listed above features behavioral analytics, bot mitigation, and
DDoS protection.
Akamai Kona Site Defender

Akamai Kona Site Defender is a web application and
API protection (WAAP) tool that automates web app security for 24/7 protection. The machine learning (ML) tunes itself to avoid false positives and reduce alert fatigue for IT professionals while providing actionable insights on actual attacks. It’s highly configurable, and Akamai provides a zero-second SLA, promising response to application-layer DDoS attacks in seconds.
AppTrana Managed Web Application Firewall

AppTrana Managed Web Application Firewall is a fully managed WAF perfect for businesses with small or non-existent internal IT departments. With continuous risk detection, organizations get real-time insights into their vulnerabilities thanks to automated scans and third-party penetration testing. And 24/7 DDoS protection keeps your site running to avoid downtime and credential theft.
Barracuda WAF
 Barracuda WAF
Barracuda WAF offers easy to use web application protection with bot and DDoS mitigation to keep business applications running smoothly and securely. The server cloaking feature prevents attackers from learning about a business’s servers before an attack, making it more difficult for them to find vulnerabilities. And the active threat intelligence provides near real-time insights thanks to machine learning, so organizations can detect and respond to threats faster.
CloudFlare WAF

CloudFlare WAF provides managed rules, giving businesses protection against both known and zero-day web-based threats. Organizations can create custom rulesets that prevent false positives and allow the system to automatically respond to common alerts. The WAF will also alert IT when sensitive information is involved in a breach, helping them prioritize serious threats and protect the organization.
Also Read:
Fastly vs. Cloudflare
F5 Advanced WAF

F5 Advanced WAF uses machine learning and threat intelligence to protect web applications from bots, DDoS attacks, and everything on the OWASP Top 10 list. In-browser data encryption prevents attackers from stealing data, while stolen credential protection blocks brute force attacks. F5 also offers mobile application protection through cookie validation, app hardening, and behavioral analysis.
Fortinet FortiWeb
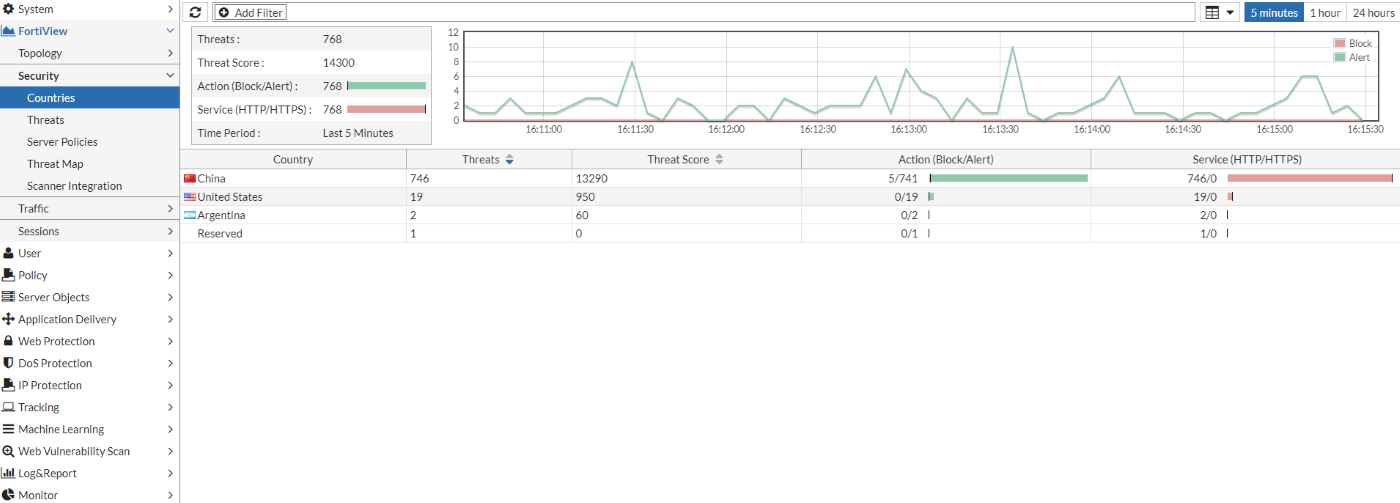 Fortinet
Fortinet FortiWeb is a web application firewall that protects a business’s changing attack surface from known and unknown threats. In addition to hardware options, there’s also a SaaS solution that doesn’t require any hardware or software, providing a helpful alternative for small and medium-sized businesses (SMBs). Using machine learning, the platform reduces false positives and identifies anomalies quickly to reduce alert fatigue and allow IT to focus on actual threats.
What are the key features of a web application firewall?
Businesses looking to protect themselves from online attacks should consider web app firewalls with the following features.
OWASP Top 10 protection
The
Open Web Application Security Project (OWASP) provides a list of the top ten security risks that web applications face. It includes vulnerabilities like broken access control, outdated components, and identification and authentication failures. WAF security should include protections against all of these threats because they’re well-known and have documented fixes.
Zero day protection
Unfortunately, we don’t currently know about all the threats that exist or will exist. Because of this, WAFs need to have protections in place for zero day threats, or threats that are currently unknown. They can do this by only allowing traffic that they know is valid and safe. If the firewall blocks a session, IT can then investigate it and decide whether or not they should whitelist it.
PCI DSS compliance
Credit card information and personal data are major targets for attackers. If you are a merchant that accepts credit card information on your website or stores it on your servers,
PCI DSS applies to you. In addition to blocking malicious traffic that comes in through your web applications, your WAF should also include PCI compliance reporting to ensure that you’re meeting the regulatory requirements.
Central monitoring and management
The web application firewall should also make it easy for your IT team to monitor and manage traffic from a single console. In a business environment, IT doesn’t have time to individually check every device to see what the WAF flagged. But if all that data is in one screen, they can quickly identify vulnerabilities and remediate them before they become a larger issue.
What are the benefits of WAF?
Web application firewalls offer businesses a lot of security benefits, especially if they rely on web applications (SaaS) for some of their operations.
Protecting internal and customer data
Web applications are often built off open source software which makes them prone to vulnerabilities if they are not updated or patched regularly. Because of this, attackers often use web apps as a gateway to get to a company’s internal intellectual property or customer information. With a WAF, however, companies can block more of this malicious traffic, safeguarding themselves and their customers.
Also Read:
Expert Panel: A Data Governance Policy That Pleases BI & SecOps
Meeting compliance requirements
Firewalls are a requirement for PCI DSS compliance. But network firewalls typically don’t extend to web applications, leaving customers’ payment information vulnerable. WAFs prevent code injections, keeping attackers from being able to skim credit card information or other personal data or direct consumers to malicious websites.
Automating part of IT’s workload
Web application firewalls automatically filter malicious traffic and block it from accessing web applications, decreasing some of the manual work that IT has to do. With WAFs, IT mainly has to monitor the system to investigate any alerts, and if a session gets blocked that shouldn’t have, they can then go in and whitelist it. A WAF is a more proactive approach to web security, keeping IT from constantly having to react to new breaches.
Also Read:
How Automated IT Management Platforms Save You Money
Trends that affect WAF
Web application firewalls don’t work in a vacuum, meaning other technology trends often affect their popularity and how they’re used.
Next-generation firewalls
Despite the improvements in traditional firewalls leading to the development of
next-generation firewalls (NGFWs), this new technology doesn’t replace WAFs as well. Instead, they work together to protect the business at different layers. NGFWs protect the organization’s network, staying close to the business while WAFs operate on the application layer, closer to the web. Additionally, an NGFW protects the users, but a WAF protects data. Companies should look for WAFs and NGFWs that work together, allowing their IT team to monitor all of the layers from a centralized console.
Growth in healthcare
Thanks to the COVID-19 pandemic,
telehealth platforms are taking off, and providers are seeing more patients and storing more records in their
EHR & EMR systems. These web applications add another vulnerability to already highly-targeted organizations, giving attackers another avenue to sensitive personal data. WAFs can help mitigate this vulnerability and reduce attacks from known malware as well as some zero day threats.
Also Read:
The Move to Mobile & HIPAA: What you Need to Know
Rise in web-based attacks
Emerging threats have strongly impacted the effectiveness of WAFs. About
65 percent of organizations found threats in their system that had bypassed their web application firewall. They require a large amount of configuration to allow them to properly defend applications, and IT as an industry is highly understaffed. However, WAFs do seem to be good at protecting mobile applications, with 54 percent of respondents calling them very effective.
As cybersecurity tools get better at filtering out known, signature-based attacks, businesses are moving towards tools that focus more on blocking zero day threats, including full
endpoint detection and response (EDR) platforms and zero trust security. However, these might not always extend to web applications and provide the level of DDoS protection that WAFs can.
Choosing the best web application firewall for your business
Companies looking for a web application firewall need to choose one that protects against both known and unknown threats and meets the compliance requirements for their organization. Additionally, it should integrate with other security tools to make it easier on IT teams to monitor the network from a single, centralized point. Unfortunately, web-based attacks aren’t going away, but WAFs can help businesses stop and spot them faster.
 Akamai Kona Site Defender
Akamai Kona Site Defender AppTrana Managed Web Application Firewall
AppTrana Managed Web Application Firewall Barracuda WAF
Barracuda WAF CloudFlare WAF
CloudFlare WAF F5 Advanced WAF
F5 Advanced WAF Fortinet FortiWeb
Fortinet FortiWeb Akamai Kona Site Defender is a web application and API protection (WAAP) tool that automates web app security for 24/7 protection. The machine learning (ML) tunes itself to avoid false positives and reduce alert fatigue for IT professionals while providing actionable insights on actual attacks. It’s highly configurable, and Akamai provides a zero-second SLA, promising response to application-layer DDoS attacks in seconds.
Akamai Kona Site Defender is a web application and API protection (WAAP) tool that automates web app security for 24/7 protection. The machine learning (ML) tunes itself to avoid false positives and reduce alert fatigue for IT professionals while providing actionable insights on actual attacks. It’s highly configurable, and Akamai provides a zero-second SLA, promising response to application-layer DDoS attacks in seconds.
 AppTrana Managed Web Application Firewall is a fully managed WAF perfect for businesses with small or non-existent internal IT departments. With continuous risk detection, organizations get real-time insights into their vulnerabilities thanks to automated scans and third-party penetration testing. And 24/7 DDoS protection keeps your site running to avoid downtime and credential theft.
AppTrana Managed Web Application Firewall is a fully managed WAF perfect for businesses with small or non-existent internal IT departments. With continuous risk detection, organizations get real-time insights into their vulnerabilities thanks to automated scans and third-party penetration testing. And 24/7 DDoS protection keeps your site running to avoid downtime and credential theft.
 Barracuda WAF offers easy to use web application protection with bot and DDoS mitigation to keep business applications running smoothly and securely. The server cloaking feature prevents attackers from learning about a business’s servers before an attack, making it more difficult for them to find vulnerabilities. And the active threat intelligence provides near real-time insights thanks to machine learning, so organizations can detect and respond to threats faster.
Barracuda WAF offers easy to use web application protection with bot and DDoS mitigation to keep business applications running smoothly and securely. The server cloaking feature prevents attackers from learning about a business’s servers before an attack, making it more difficult for them to find vulnerabilities. And the active threat intelligence provides near real-time insights thanks to machine learning, so organizations can detect and respond to threats faster.
 CloudFlare WAF provides managed rules, giving businesses protection against both known and zero-day web-based threats. Organizations can create custom rulesets that prevent false positives and allow the system to automatically respond to common alerts. The WAF will also alert IT when sensitive information is involved in a breach, helping them prioritize serious threats and protect the organization.
Also Read: Fastly vs. Cloudflare
CloudFlare WAF provides managed rules, giving businesses protection against both known and zero-day web-based threats. Organizations can create custom rulesets that prevent false positives and allow the system to automatically respond to common alerts. The WAF will also alert IT when sensitive information is involved in a breach, helping them prioritize serious threats and protect the organization.
Also Read: Fastly vs. Cloudflare
 F5 Advanced WAF uses machine learning and threat intelligence to protect web applications from bots, DDoS attacks, and everything on the OWASP Top 10 list. In-browser data encryption prevents attackers from stealing data, while stolen credential protection blocks brute force attacks. F5 also offers mobile application protection through cookie validation, app hardening, and behavioral analysis.
F5 Advanced WAF uses machine learning and threat intelligence to protect web applications from bots, DDoS attacks, and everything on the OWASP Top 10 list. In-browser data encryption prevents attackers from stealing data, while stolen credential protection blocks brute force attacks. F5 also offers mobile application protection through cookie validation, app hardening, and behavioral analysis.
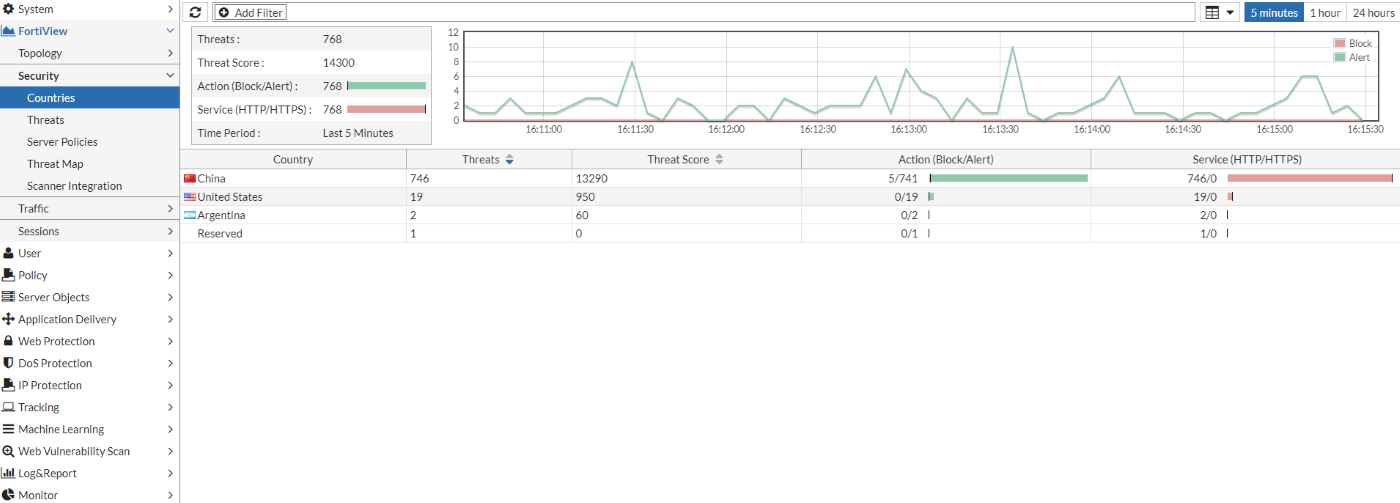 Fortinet FortiWeb is a web application firewall that protects a business’s changing attack surface from known and unknown threats. In addition to hardware options, there’s also a SaaS solution that doesn’t require any hardware or software, providing a helpful alternative for small and medium-sized businesses (SMBs). Using machine learning, the platform reduces false positives and identifies anomalies quickly to reduce alert fatigue and allow IT to focus on actual threats.
Fortinet FortiWeb is a web application firewall that protects a business’s changing attack surface from known and unknown threats. In addition to hardware options, there’s also a SaaS solution that doesn’t require any hardware or software, providing a helpful alternative for small and medium-sized businesses (SMBs). Using machine learning, the platform reduces false positives and identifies anomalies quickly to reduce alert fatigue and allow IT to focus on actual threats.


